To effectively run a cybersecurity and privacy program, you’ll need to build core cybersecurity and privacy policies that govern these...
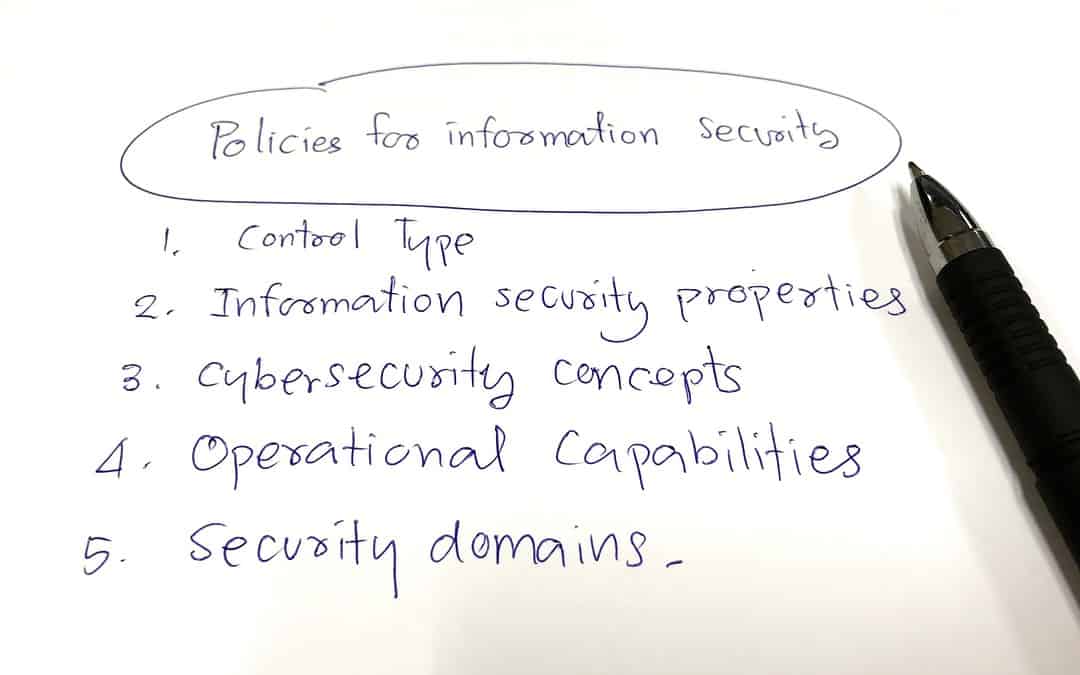
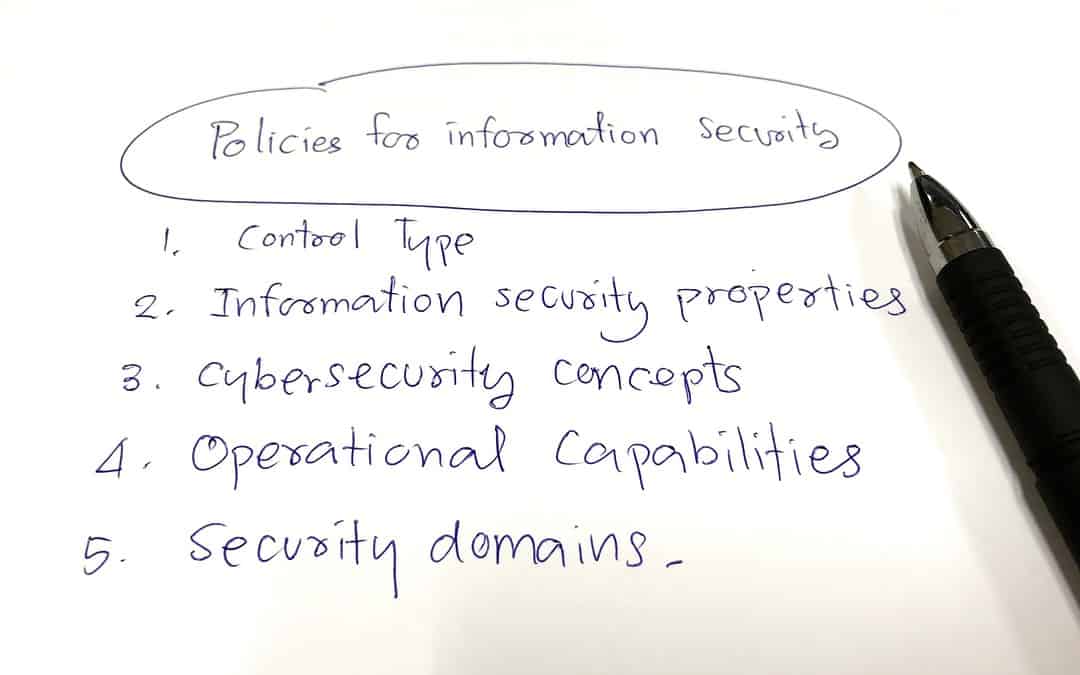
To effectively run a cybersecurity and privacy program, you’ll need to build core cybersecurity and privacy policies that govern these...

Penetration Testing Definition A penetration test, which is often shortened to “pen test,” is essentially a fake cyberattack. It is...

This series of posts presents a survey of the privacy regulations that you’ll need to understand in order to protect your business. We’ll...

Asia, in its vastness and complexity, doesn’t lend itself to a continental overview. In this post, we'll look at the Asia-Pacific Economic...
Over the past twenty years, privacy legislation in Africa has been gaining momentum; 33 countries in the continent now having some form of...

As much as the GDPR is the 800-pound gorilla in European data privacy regulations, there are countries that are currently outside of its...

Three quarters of us don’t trust businesses to do the right thing with our emails, phone numbers, preferences and bank details. I find...

In a previous post, we gave an overview of data privacy legislation in the United States, both federal and state. We’ll discuss our North...

If your business is located in the United States or does business there, allow us to introduce you to the alphabet soup of regulators that...