To effectively run a cybersecurity and privacy program, you’ll need to build core cybersecurity and privacy policies that govern these functions. These policies are critical in that they impact a wide swath of functions—from prevention to resilience and from identification to recovery.
Unlike many organizational policies that “come down from the mountain,” cybersecurity and privacy policies are derived following a substantial amount of discovery and assessment work.
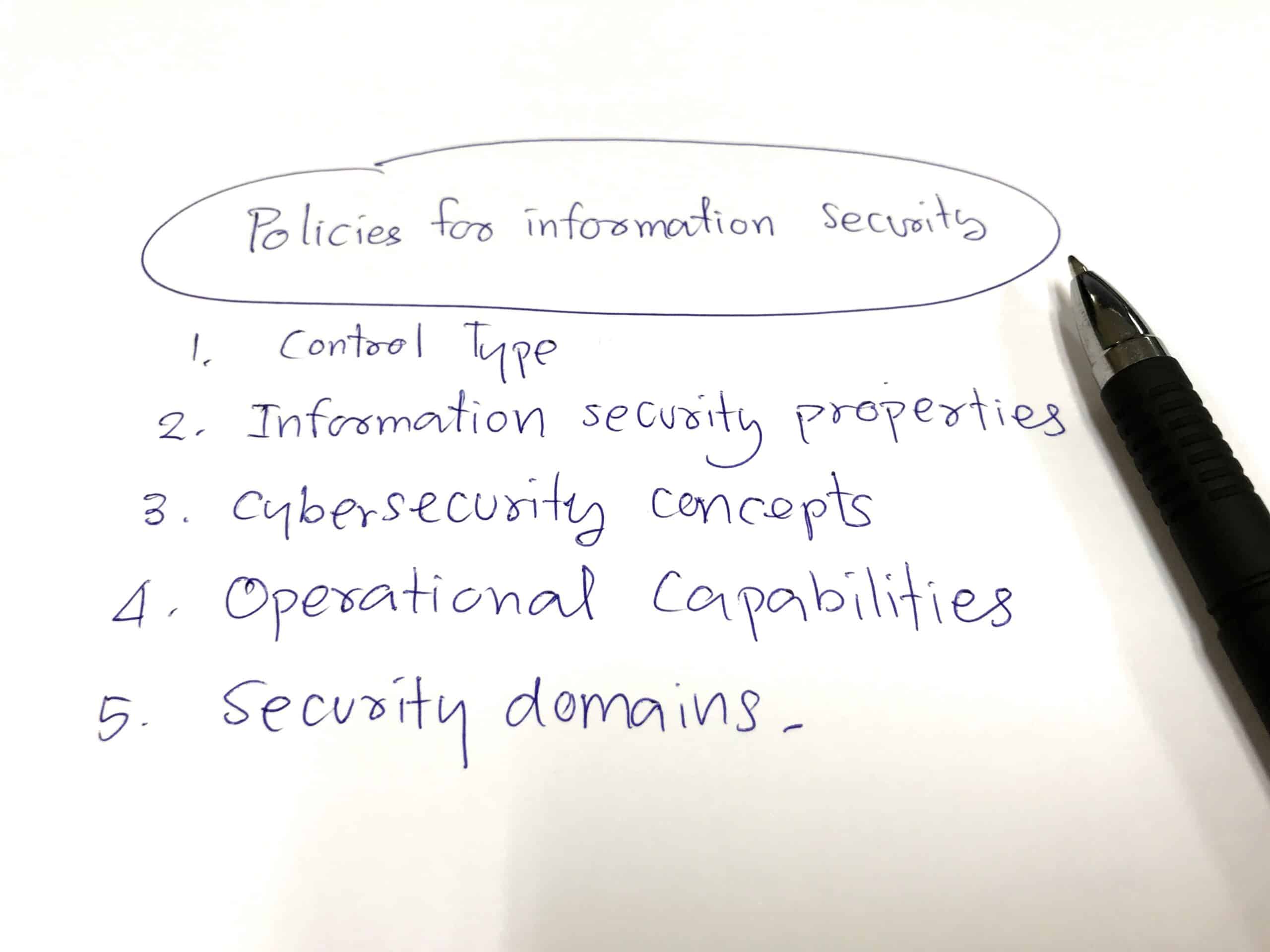
What is a Cybersecurity Policy?
A cybersecurity policy provides guidelines for employees for how to access data and organizational assets.
Steps for Creating a Cybersecurity Policy
A number of things must happen before such policies even make it to the draft table:
1. Asset identification
2. Conduct a risk assessment
3. Document the operational cybersecurity procedures
1. Asset Identification.
First and foremost, you must go through an asset identification and valuation process. Only then will you know what you are protecting and for how much.
2. Conduct a risk assessment.
Second, you must assess your risks. Essentially, “who’s out to get you (or your data)?” But the concept of risk extends beyond getting hacked. Also consider industry-specific risks, regulatory-specific risks, compliance requirements, and data-specific threats (e.g., personally identifiable information).
3. Document the operationl cybersecurity procedures.
Third, document the operational cybersecurity and privacy policies and procedures. These will be “rolled up” into the overall cybersecurity and privacy policies and referred to by them.
With these three things in place, you can now focus in creating the top-level policies that govern your cybersecurity and privacy programs. These policies will reflect your company’s specific requirements and capabilities. They will address everything from operating procedures to reporting and recovery, user training, and asset monitoring, testing, and auditing.
Make sure that the policies are not only distributed far and wide, but also are understood and supported by everyone in the organization. Cybersecurity and privacy are everyone’s responsibility. These policies need to reflect that responsibility and help enable everyone to conduct business safely.
Do you need help with your policies and procedures in your organization? Get in touch with us. We can help you develop a set of policies that will ensure your cybersecurity resilience.

0 Comments