“We don’t know what we don’t know,” said our client, somewhat embarrassed. They had spent a lot of money on cybersecurity tools, staff,...


“We don’t know what we don’t know,” said our client, somewhat embarrassed. They had spent a lot of money on cybersecurity tools, staff,...

As the “arms race” between hackers and security experts intensifies, cyber compliance standards have become increasingly complex. The...

If you’re reading this article, you’re well along on your journey to understanding cybersecurity and privacy programs. Still, it’s a...

Before you begin developing (or fixing!) your cybersecurity program, make sure you know the fundamentals. This material, adapted from my...

In the post “The Basics of Controls,” you read about different types of controls. Before you can do anything with all that knowledge, you...

Long before antivirus software was a twinkle in an engineer’s eye, humans were employing various strategies to protect their valuables...

In Passwords 101, we looked at what is likely your first line of defense against cyberattack: the humble password. There are a lot of...
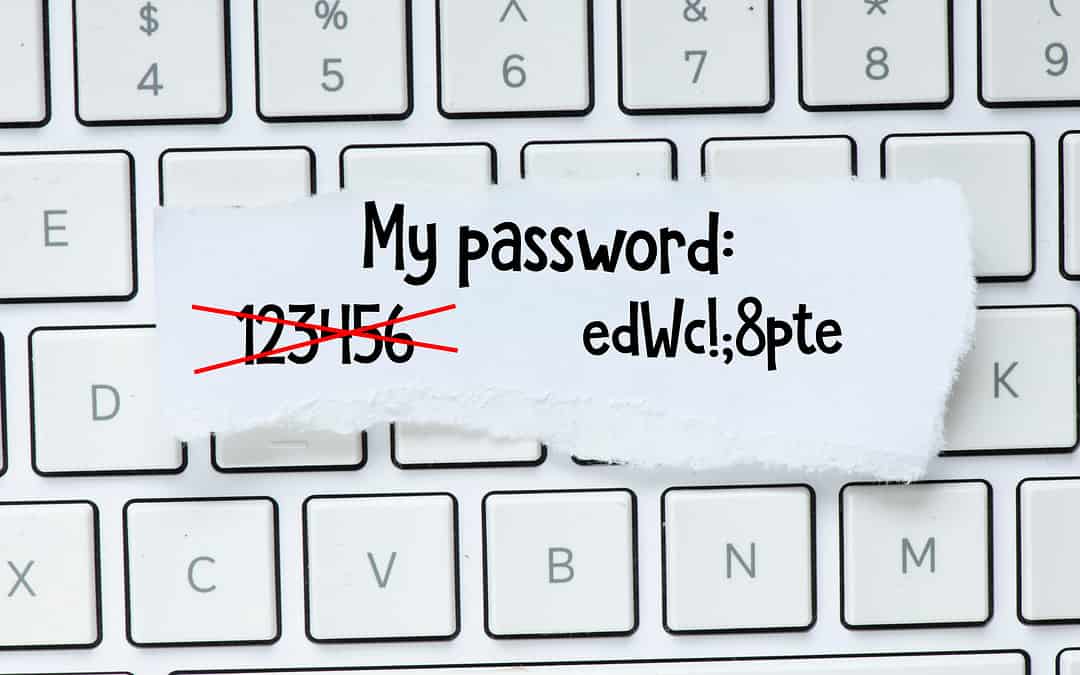
Like death and taxes, passwords are an inescapable part of our lives these days, both in and out of the office. Did you ever hear the joke...

In our first post on Talking Tech, we covered a few of the most basic terms that come up in conversations about information technology....