Like death and taxes, passwords are an inescapable part of our lives these days, both in and out of the office. Did you ever hear the joke about bad passwords? It goes, “I always have trouble remembering my password so I changed it to incorrect. That way, when I enter it wrong, the computer will say, “Your password is incorrect.”
But cybersecurity experts aren’t laughing. So let’s talk about what makes a good password, what makes a terrible one, and what you can do to practice good password hygiene.
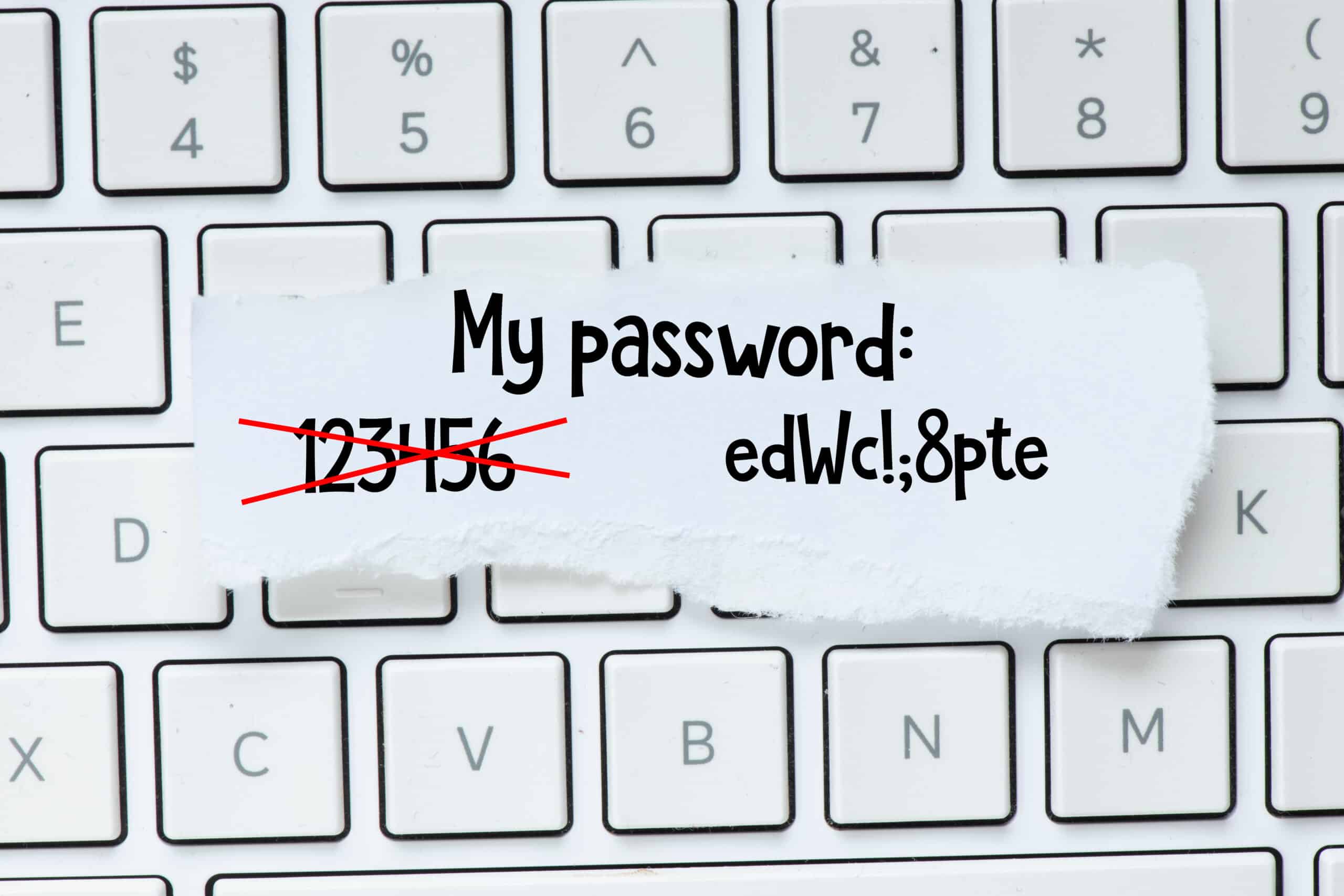
Even in 2022, people depend on too-easily guessed, too-often repeated passwords. According to research conducted by the security company Nordpass, in 2021 the three most popular passwords in the United States were “123456,” “password,” and—wait for it—“12345.” (By the way, if one of those passwords looks eerily familiar to you, please stop reading and go change it immediately!)
It seems to make no difference how often cybersecurity nerds complain about bad passwords… people keep using them.
There are likely a number of reasons for this. Laziness, for sure—let’s be honest, with so many sites and applications requiring passwords, it’s understandable why users don’t want to bother with complex codes.
But another factor relates to a fundamental misunderstanding about how hacks happen. Many “civilians” assume that cracking passwords always involves some sort of undefeatable evil genius supercomputer that runs through thousands of passwords per second until the correct code is discovered through process of elimination. This leads to a sense of fatalism. “What, me worry?” says Alfred E Newman-ish users, “It’s a waste of time; I’m going to get hacked anyhow.”
The above scenario is called a brute-force attack and yes, unfortunately, that situation can occur. However you are likely underestimating how often security breaches occur in much simpler, low-tech ways. For example, one of the most common ways for a hacker to get your password is to literally just buy it online. (They don’t call it the Dark Web because of all the nice things happening there.)
You’ve surely heard those news stories about massive companies experiencing equally massive data breaches. Well, what do you think happens to all that stolen personal information? It gets sold, that’s what happens. Other hackers purchase the data and use it to pry open savings accounts, credit card accounts, etcetera etcetera. Sometimes the bad guys buy email passwords; once they’ve opened a user’s Outlook account, they help themselves to whatever information they need to get at their victim’s money.
Consider this question: what is one small thing you could do, right now, that would render all that stolen data useless?
Yes, change your passwords. Hackers can’t exploit a password that hasn’t been stolen.
And if you’re thinking, “Thanks, Captain Obvious,” you should know that more than half of Americans surveyed by the firm LogMeIn hadn’t changed their password in over a year, even after they’d heard about a security breach in the news.
Past Password Recommendations
Experts used to recommend changing all your passwords about as often as you change your toothbrush. Fortunately, that’s no longer considered necessary. However, if you have any reason to believe a password has been compromised—whether due to a publicized security breach or strange activity on one of your accounts—you’d best get to work changing your passwords, and soon. Sounds like a pain, but you know what’s much more painful? Identity theft.
Common Password Errors
1. Same password for multiple accounts.
In addition to keeping exposed passwords, another huge pitfall is using the same password for multiple accounts. The problem here should be obvious: if you are using, as it were, One Password to Rule Them All, then all it takes is the release of that single password to unravel your entire life. Or for our IT managers out there, your entire company. But while it “should” be obvious, LogMeIn found that roughly 2/3rds of Internet users were using the same passwords for more than one site or application.
2. Dictionary attack.
Another very basic way hackers can come for your data is called a dictionary attack, which is pretty much what it sounds like: special software runs through a list of standard words, searching for the one that might unlock an account. This is why security experts discourage the use of not only “password” and “incorrect,” but any garden-variety words or names.
3. Phising.
A third avoidable trap is phishing, which is a catch-all term referring to a variety of methods hackers use to trick you into handing them the keys to your online identity. Hopefully by now you have already been told never to take candy from strangers—“candy” in an email context meaning unknown attachments or links. But, since even in 2022 we still hear of people falling for scam emails, forgive us if we repeat this advice: please do not click on links or attachments in emails from people you don’t know.
To this sage advice, let us also add: do not click on links in emails that might or might not be from a bank or credit card company. If you have a question about your account, consult the account directly on your own, not via a link that may be seeking your personal information or recording your keystrokes. And never click on links that claim to be from the Internal Revenue Service. As a matter of policy, the IRS never emails people links. (Even in 2022, the IRS conducts business the old-fashioned way, by means of terrifying letters to your physical mailbox.)
Also be wary of those “fun” surveys on websites or Facebook—those could also be phishing attempts. Posts with headlines like, “I Bet I Can’t Guess the Name of Your First Pet” are not entertainment; they are ham-handed attempts to get users to reveal the answers to common security questions. Strangers on Facebook should not be trusted with details about your high school, your first car, or the maiden name of your sainted mother.
Passwords are like underwear: make them personal, make them exotic, and change them on a regular basis
—Overheard at SecureWorld Atlanta
How to Create a Strong Password
Okay, that’s a lot of things not to do. So let’s switch gears and talk about what you should do. Here are some tips that security experts agree can help keep your passwords safer.
1. Meaningful password, but not obvious.
When creating your own passwords, use a phrase that is meaningful to you but not obvious to others: YouPuttheLimeintheCoconut, for example. Or even better, YouPuttheLimeintheC0c0nut!Do you see what we did there? We swapped the o’s for zeroes, and we added an exclamation point. Using numbers and symbols adds another layer of protection, because it expands the number of variables a hacker would have to attempt in order to find the exact password.
2. Try encrypted sentence method.
Since expanding the number of variables is the name of the game here, try the encrypted sentence method, which uses the first letters of a phrase instead of complete words: as in, YPtLitC! Of course, now the password has become a little short, and we lost the zeros from the example above. So how about YPtLitC0c0nut! Now you have a password that looks like gibberish but is in fact an ode to a Harry Nilsson classic from the 1970s. Take that, hackers.
3. Use for only one account.
As awesome as our new Harry Nilsson password obviously is, you should only use it for one account, not all of them. Remember, having a hard-to-hack password is great, but if your bank gets hit with a massive data breach, your gorgeous password could end up on the Dark Web anyway. Variety isn’t just the spice of life—it’s also the ticket to increased online safety.
4. Have a password manager.
Consider using a password manager. These are dozens of programs that will create and store extremely strong passwords on your behalf. Some of the better ones include LastPass, BitWarden, and ZohoVault. Yes, setting up a password manager can take a little effort, but the payoff is huge.
Passwords Still Have Problems
Here’s the last thing we want to say about passwords, and unfortunately it’s a little bit of a bummer. We all have a tendency to overestimate them.
It’s not that passwords aren’t important—they definitely are. Whether you run a large company, a small IT department, or your own home-based LLC, you owe it to yourself to practice good password hygiene and make sure that all employees do, too.
But if passwords were enough to keep your assets protected, there’d be no need for trillions of dollars in cybersecurity spending, no ongoing threats, and no sleepless nights fighting hackers. And there certainly wouldn’t be a need for a solution like cyberCTRL. So yes, we need good passwords, but when it comes to cybersecurity at the business level—passwords are just the beginning. Privacy and cybersecurity program development is not for the faint of heart, but with the right guidance, you can start off on the right foot.
Articles on this blog (and plenty of others!) can help you dip your toe into the cybersecurity pond. But for a deeper level of expertise, please give us a call.

0 Comments